
A computer incident report is a crucial document for documenting security breaches, system failures, and other incidents that may impact an organization's data and operations. It serves as a record of events, facilitates investigations, and helps to identify and address vulnerabilities. A well-structured computer incident report template provides a clear and consistent framework for reporting incidents, ensuring that all relevant information is captured and analyzed effectively. This template is designed to be adaptable to various types of incidents, from minor software glitches to more serious security breaches. Computer Incident Report Template is more than just a form; it's a proactive tool for safeguarding your organization's digital assets. This comprehensive guide will walk you through creating a robust incident report template, covering essential elements and best practices.
Understanding the Importance of Computer Incident Reports
The rise of cyber threats has made it increasingly vital for organizations to have a documented process for handling security incidents. Computer Incident Report Template isn't just about compliance; it's about mitigating risk, demonstrating due diligence, and protecting your reputation. Without a clear record of incidents, it's difficult to determine the scope of the problem, identify root causes, and implement effective preventative measures. Furthermore, timely reporting allows for rapid response and containment, minimizing potential damage and disruption. A properly executed incident report can be the difference between a minor incident being quickly resolved and a major breach leading to significant financial and reputational consequences.
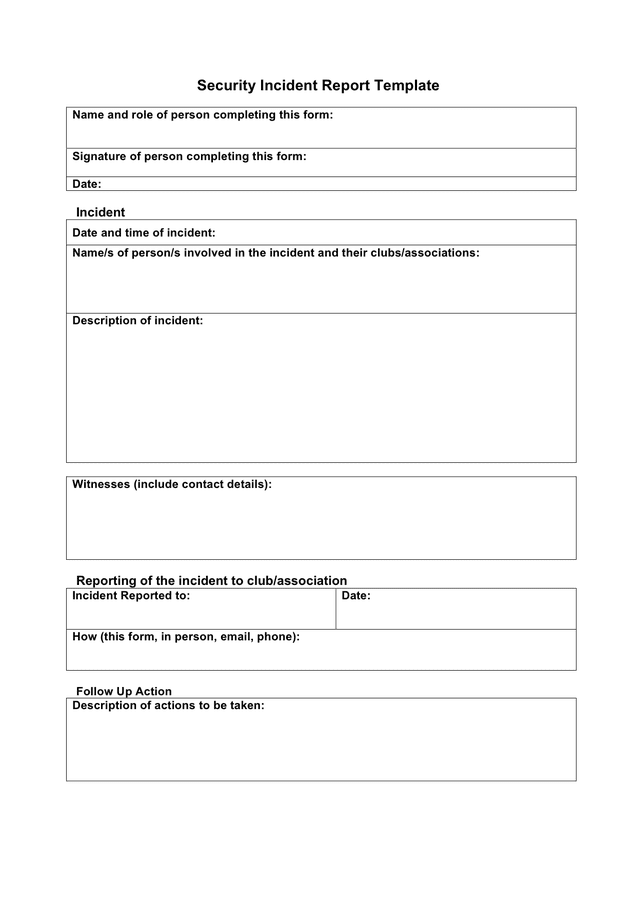
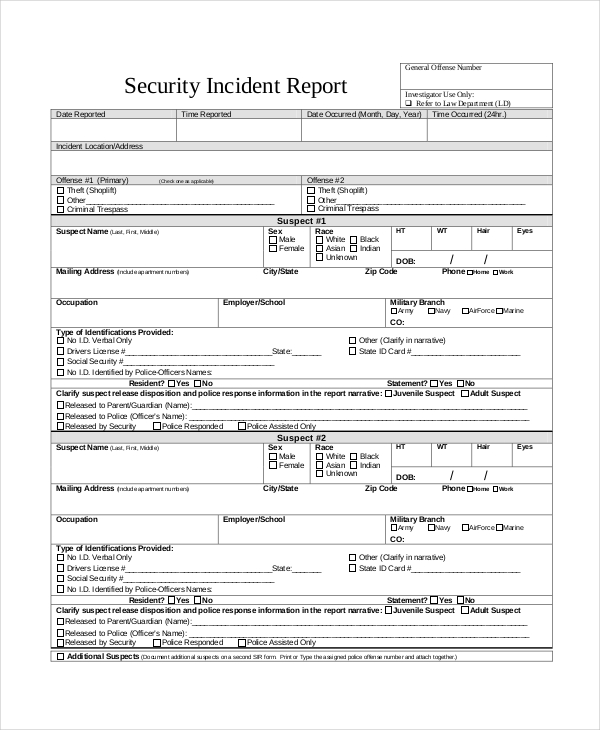
Key Elements of a Comprehensive Computer Incident Report Template
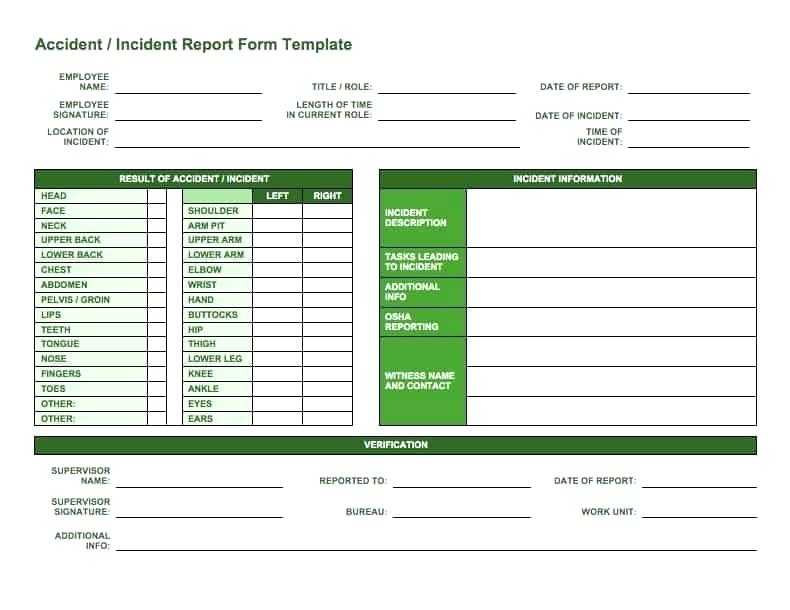
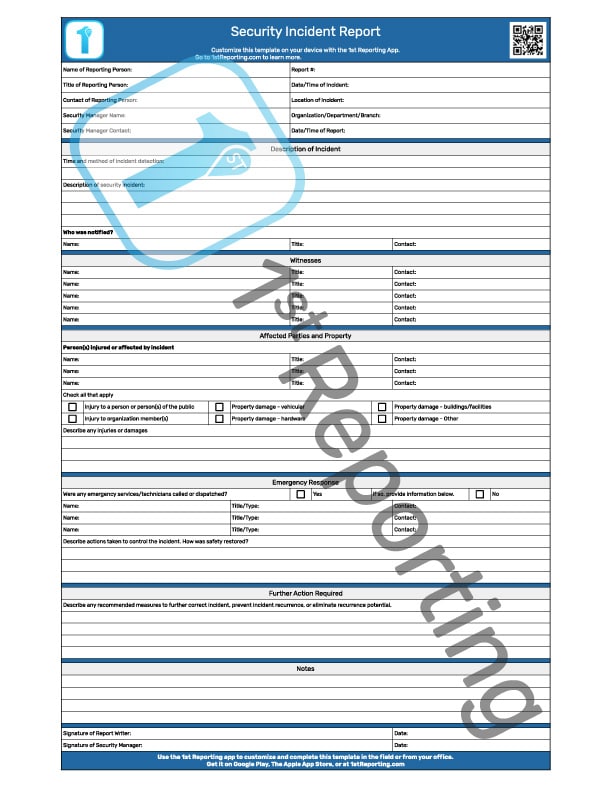
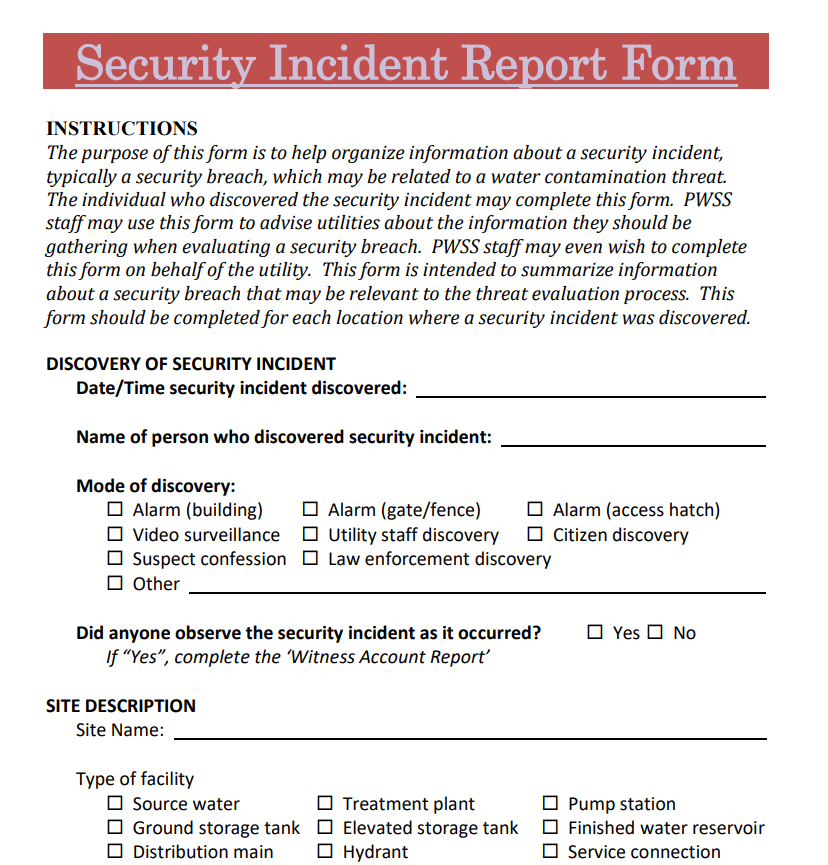
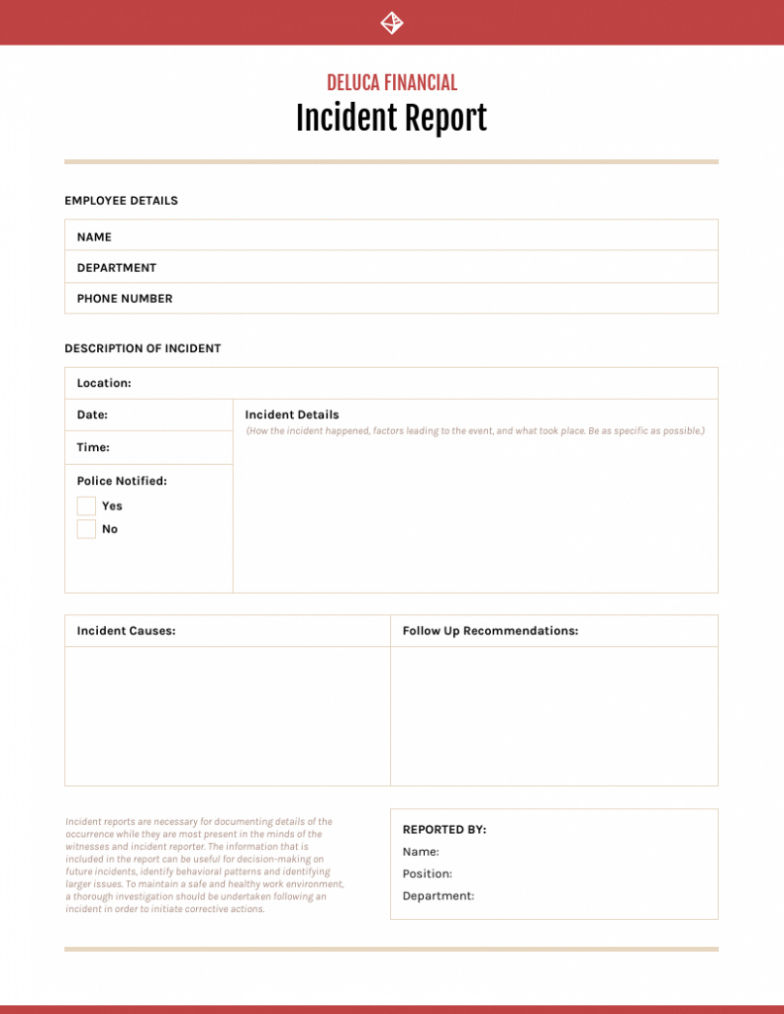
A solid computer incident report template typically includes the following key elements:

- Incident Title: A concise and descriptive title that accurately reflects the nature of the incident.
- Date and Time of Incident: Precise timestamp is essential for tracking and analysis.
- Reporting Party: The name and contact information of the individual responsible for reporting the incident.
- Affected Systems/Devices: A detailed list of all systems, devices, or applications that were affected by the incident.
- Description of Incident: A chronological account of what happened, including the sequence of events. Be specific and avoid vague language.
- Impact Assessment: A clear explanation of the consequences of the incident, including data loss, system downtime, financial losses, and reputational damage.
- Evidence Collected: A summary of the evidence that was gathered during the investigation, such as logs, screenshots, and forensic data.
- Root Cause Analysis (RCA): A preliminary analysis of the underlying cause of the incident. This is a critical step in preventing future occurrences.
- Remediation Actions Taken: A description of the steps taken to address the incident and restore systems to normal operation.
- Preventative Measures: Recommendations for preventing similar incidents from occurring in the future.
- Follow-up Actions: A timeline of follow-up activities, such as testing, patching, and security audits.
Section 1: Incident Details – The Core of the Report
This section is the foundation of your incident report. It provides a detailed account of the event itself.
- Description: Start with a clear and concise description of the incident. Avoid jargon and technical terms unless they are necessary for understanding. Focus on the what and when. For example, instead of "The system experienced a denial-of-service attack," write "On July 26, 2024, at 14:30 PST, our monitoring system detected a sustained denial-of-service attack originating from IP address 192.168.1.100 targeting the production web server. The attack lasted for 30 minutes."
- Affected Systems/Devices: List all systems, devices, or applications that were impacted. Include specific model numbers and serial numbers if available. Categorize affected systems (e.g., servers, workstations, network devices).
- Timeline: Create a chronological timeline of events leading up to, during, and after the incident. This helps to understand the progression of the problem. Use a table format for clarity.
- Log Data: Include relevant log data from affected systems. Screenshots are also valuable. Ensure log files are properly preserved and accessible.
- User Impact: Document any user impact, including affected users, the type of data accessed, and any actions taken by the user.
Section 2: Impact Assessment – Quantifying the Damage
This section focuses on the consequences of the incident. It's crucial to understand the extent of the damage.

- Data Loss: Quantify any data loss, including the amount of data affected and the time period during which it was lost. Note any data encryption methods used.
- System Downtime: Record the duration of system downtime and the impact on business operations.
- Financial Loss: Estimate the financial impact of the incident, including costs associated with data recovery, system repair, legal fees, and lost revenue.
- Reputational Damage: Assess the potential impact on the organization's reputation, considering factors such as customer trust and brand image.
- Business Continuity: Evaluate the impact on business continuity, including the ability to continue operations and maintain essential services.
Section 3: Root Cause Analysis – Uncovering the Underlying Cause
This section is where you delve into why the incident occurred. Don't just focus on the symptoms; identify the root cause.
- Potential Causes: Brainstorm potential causes of the incident, considering factors such as software vulnerabilities, misconfigurations, human error, or external attacks.
- Vulnerability Assessment: If possible, identify any vulnerabilities that contributed to the incident.
- Root Cause Diagram: Create a visual representation of the root cause analysis, using a diagram to illustrate the relationships between the various factors.
- Corrective Actions: Outline the steps taken to address the root cause of the incident.
Section 4: Remediation and Prevention – Moving Forward
This section details the actions taken to resolve the incident and prevent future occurrences.
- Remediation Steps: Describe the steps taken to restore systems to normal operation, including patching, configuration changes, and data recovery.
- Security Enhancements: Outline any security enhancements that were implemented to prevent similar incidents from occurring in the future.
- Security Policies: Review and update security policies and procedures to address any weaknesses identified during the investigation.
- Training and Awareness: Assess the effectiveness of security awareness training and identify any gaps.
Section 5: Appendices – Supporting Documentation
This section includes any supporting documentation that is relevant to the incident report.
- Log Files: Include copies of relevant log files.
- Screenshots: Provide screenshots of affected systems, applications, and data.
- Forensic Data: Include any forensic data that was collected during the investigation.
- Incident Response Plan: Reference the incident response plan that was executed.
Conclusion – Lessons Learned and Future Considerations
A well-documented computer incident report is an invaluable tool for organizations seeking to improve their security posture. By systematically documenting incidents, analyzing their root causes, and implementing effective preventative measures, organizations can significantly reduce their risk of future breaches. Computer Incident Report Template is a dynamic document that should be regularly reviewed and updated to reflect changes in the organization's environment and security practices. Continuous monitoring, proactive threat intelligence, and a strong security culture are essential for maintaining a resilient and secure digital infrastructure. Ultimately, a proactive approach to incident management, informed by thorough reporting, is the key to safeguarding your organization's valuable data and assets.
0 Response to "Computer Incident Report Template"
Posting Komentar