When a piece of hardware reaches the end of its life, simply deleting files is not enough to protect the sensitive information it once held. For any organization serious about data security and regulatory compliance, proving that data-bearing assets have been properly destroyed is a critical final step. This is where a comprehensive Hard Drive Destruction Certificate Template becomes an indispensable tool, serving as a formal record that documents the secure and permanent disposal of storage media. This certificate acts as a legal receipt, providing a verifiable audit trail that confirms data has been rendered unrecoverable.
The Certificate of Destruction, often abbreviated as CoD, is far more than a simple piece of paper. It is a legally binding document that provides tangible proof of your due diligence in safeguarding confidential data. In an era of rampant data breaches and stringent privacy laws, being able to produce this documentation can be the difference between demonstrating compliance and facing severe penalties. It provides peace of mind to stakeholders, customers, and regulatory bodies, assuring them that private information related to clients, employees, and company trade secrets has been handled responsibly from creation to final destruction.

This formal documentation is crucial for a wide range of entities. Large corporations, healthcare providers bound by HIPAA, financial institutions, and government agencies all rely on these certificates to close the loop on their data lifecycle management policies. Similarly, IT Asset Disposition (ITAD) vendors who perform destruction services issue these certificates to their clients as a standard part of their process. For any business, regardless of size, understanding the components and significance of a destruction certificate is a fundamental aspect of modern cybersecurity and risk management.
This guide will delve into every facet of the hard drive destruction certificate. We will explore its essential components, its profound legal importance, and how to effectively use a template to create a robust and defensible record. By understanding what makes a certificate truly secure and compliant, you can ensure your organization's data disposal processes are not just effective, but also thoroughly documented and auditable, protecting you from future liabilities and reinforcing your commitment to data privacy.
Understanding the Certificate of Destruction (CoD)
A Certificate of Destruction (CoD) for hard drives is a formal document that serves as official proof that one or more storage devices have been securely and irreversibly destroyed. It acts as an official record in a company's data management and compliance archives. The primary purpose of the CoD is to create a detailed audit trail, confirming that an organization has followed established protocols for data disposal and has taken the necessary steps to prevent sensitive information from falling into the wrong hands. This document effectively terminates the chain of custody for a given asset, marking its official end-of-life.
It's important to distinguish between different methods of data sanitization. Data wiping involves using software to overwrite existing data, which can be effective but may not be sufficient for high-security information. Degaussing uses a powerful magnetic field to erase the data, rendering the drive inoperable. Physical destruction, however, is the most secure method, involving processes like shredding, crushing, or pulverizing the hard drive platters into tiny, irrecoverable fragments. A CoD is especially critical for physical destruction, as it documents the tangible, irreversible end of the device itself.

The certificate is the capstone of a secure chain of custody process. Chain of custody refers to the chronological documentation or paper trail, showing the seizure, custody, control, transfer, analysis, and disposition of physical or electronic evidence. From the moment a hard drive is decommissioned to the moment it is destroyed, every step should be tracked. The CoD is the final entry in this log, validating that the process was completed successfully and according to industry standards and legal requirements.
Why a Hard Drive Destruction Certificate is Non-Negotiable
In today's data-driven world, properly disposing of old hard drives is not just a best practice; it's a critical business function with significant legal and financial implications. A formal Certificate of Destruction is the ultimate proof that this function was performed correctly.

Legal and Compliance Requirements
Many industries are governed by strict data protection regulations that mandate the secure disposal of sensitive information. A CoD is a primary tool for demonstrating compliance with these laws.

- HIPAA (Health Insurance Portability and Accountability Act): Healthcare organizations must protect patient health information (PHI). A CoD proves that drives containing PHI were destroyed in a compliant manner.
- GDPR (General Data Protection Regulation): This EU regulation gives individuals the "right to be forgotten." A destruction certificate provides evidence that a company has fulfilled requests to erase personal data.
- FACTA (Fair and Accurate Credit Transactions Act): This act requires the secure disposal of consumer information. A CoD helps financial institutions and other businesses prove they have met FACTA's disposal rule.
- Sarbanes-Oxley (SOX): For public companies, SOX mandates strict record-keeping and data security controls. Destruction certificates are part of a robust internal control framework.
Without this documentation, an organization has no defensible proof during an audit or investigation, potentially leading to massive fines and legal action.
Mitigating Risk and Liability
A single data breach can cost a company millions in fines, legal fees, and reputational damage. If a discarded hard drive is found to contain sensitive data, the original owner is held liable. A properly executed Certificate of Destruction from a certified vendor effectively transfers that liability. It demonstrates that you took all reasonable measures to protect the data, a key principle of due diligence. This document can be a crucial piece of evidence in your defense if a breach is ever alleged.

Maintaining a Secure Audit Trail
For internal governance and security audits, a complete and accurate record of an asset's lifecycle is essential. The CoD provides a definitive end-point for every data-bearing device. This allows IT and security teams to track assets from procurement to disposition, ensuring no device goes unaccounted for. This systematic tracking, documented by the CoD, is a cornerstone of a mature IT Asset Disposition (ITAD) program and a strong overall security posture.
Key Components of a Hard Drive Destruction Certificate Template
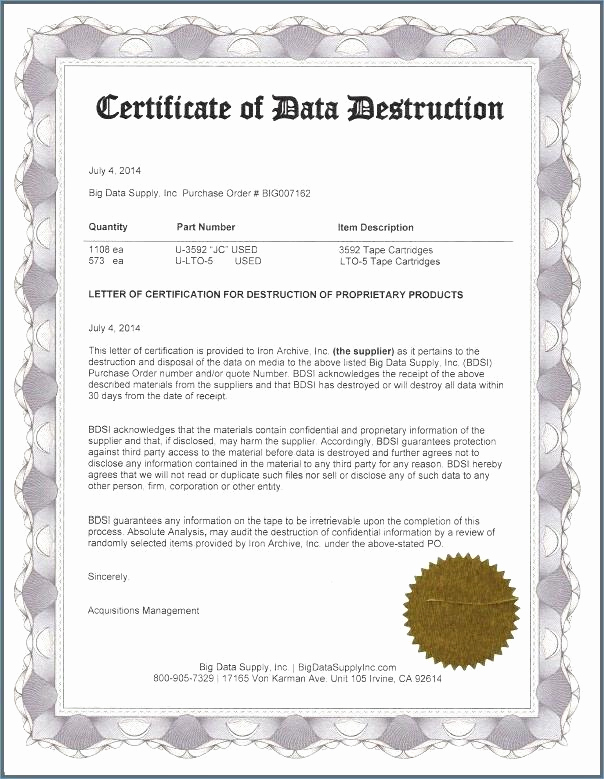
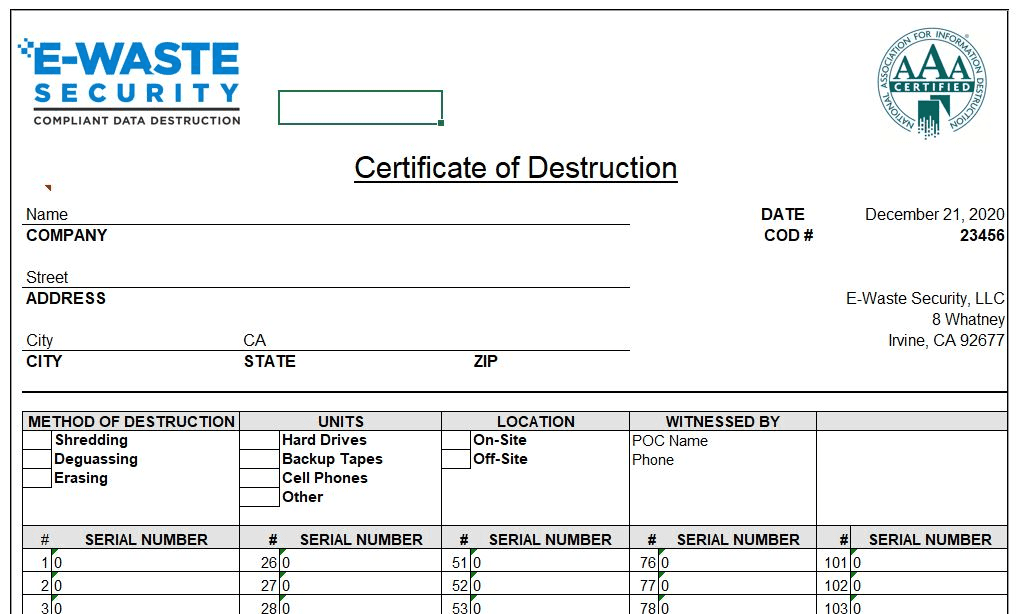
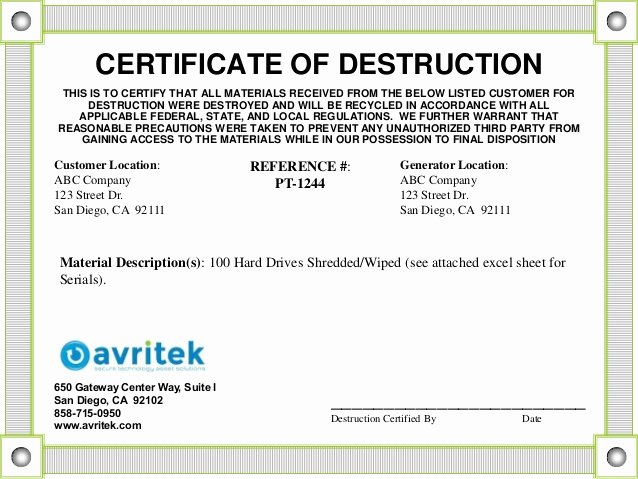
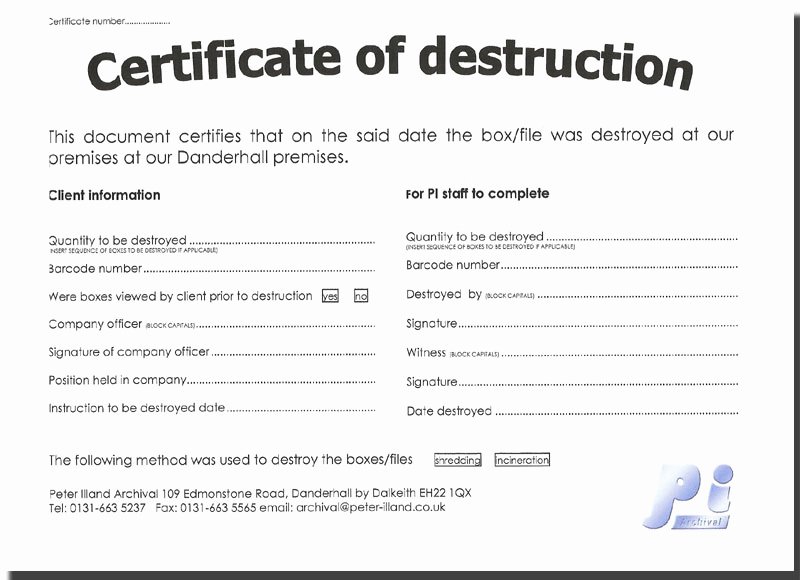
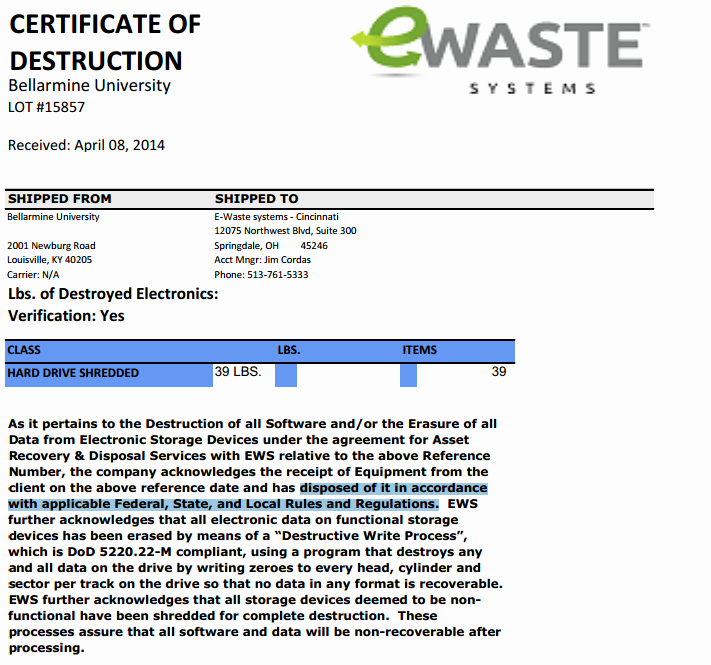
A legitimate and defensible certificate is not just a generic statement; it must contain specific, detailed information. A high-quality Hard Drive Destruction Certificate Template should include dedicated fields for each of the following critical components.

Unique Certificate Identifier
Every CoD should have a unique serial number or reference ID. This allows the document to be tracked and referenced easily in an audit. It prevents fraudulent duplication and ensures each destruction event has a distinct record.
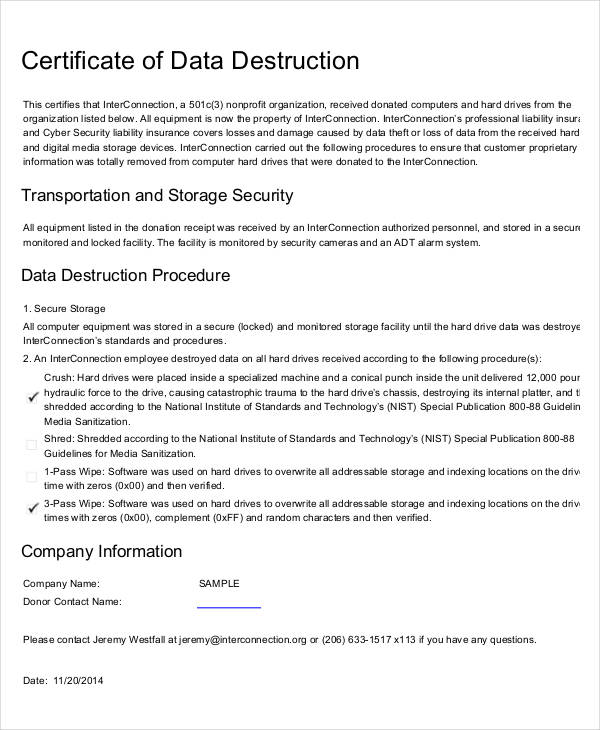
Customer Information
This section clearly identifies the owner of the data-bearing assets. It must include the full legal name of the organization, its physical address, and the name and title of the primary contact person who authorized the destruction.
Data Destruction Vendor Details
The certificate is only as credible as the company that issues it. This section must contain the full name, address, and contact information of the ITAD vendor performing the destruction. If the vendor holds certifications like NAID AAA, this should also be noted.
Chain of Custody Details
To be fully defensible, the document should reference the chain of custody. This includes the date the assets were transferred from the client to the vendor, the personnel involved in the transfer, and the location where the assets were held prior to destruction. This creates an unbroken and verifiable trail.
Detailed Asset List
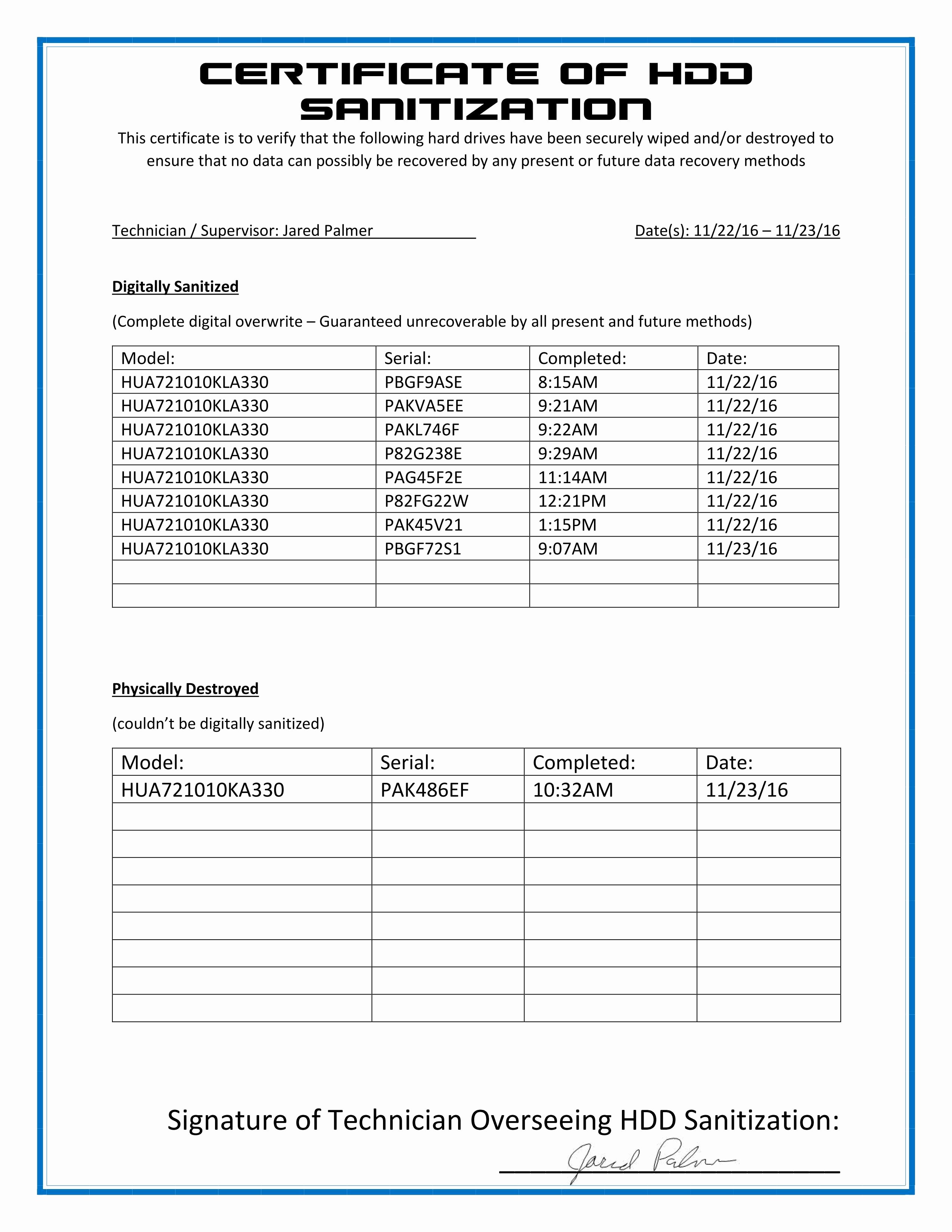
This is arguably the most crucial part of the certificate. A generic statement like "100 hard drives destroyed" is insufficient. A proper CoD must list each individual asset that was destroyed. This is typically done in an attached appendix and should include:
- Serial Number: The unique manufacturer serial number of each hard drive.
- Asset Tag: The internal asset tag number assigned by the organization.
- Make and Model: The manufacturer (e.g., Seagate, Western Digital) and model of the drive.
This level of detail ensures there is no ambiguity about exactly which devices were destroyed.

Method of Destruction
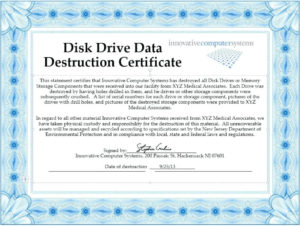
The certificate must explicitly state how the drives were destroyed. Vague terms are not acceptable. It should specify the technique, such as shredding to a specific particle size (e.g., 2mm), pulverizing, or incineration. It should also state the standard to which the destruction complies, such as the NIST 800-88 "Purge" or "Destroy" guidelines.
Date and Location of Destruction
The document must clearly state the exact date (and ideally, time) when the destruction occurred. It should also specify the physical address of the secure facility where the destruction took place.
Witness and Authorization Signatures
Finally, the certificate must be signed and dated by an authorized representative of the destruction vendor. This signature attests that all information on the certificate is true and accurate. In some cases, a representative from the client organization may also witness the destruction and provide a co-signature.
How to Use and Customize Your Template
Once you have a comprehensive template, putting it into practice requires diligence and precision to ensure the final document is accurate and legally sound.
Step 1: Choosing the Right Template
Select a template that includes all the key components listed in the previous section. Look for a professional layout that is clear and easy to read. Many ITAD vendors provide their own certified templates. If you are creating your own for internal, self-certified destruction, ensure it is robust enough to stand up to scrutiny. A downloadable Hard Drive Destruction Certificate Template can be a great starting point, but always verify it contains the necessary fields for compliance.
Step 2: Filling in the Details Accurately
The value of a CoD is in its accuracy. Double-check every piece of information before finalizing the document. The most common and critical errors occur in transcribing serial numbers. Use a barcode scanner to capture serial numbers and asset tags whenever possible to minimize human error. An incorrect serial number could render the certificate useless for that specific device in an audit.
Step 3: Integrating the Certificate into Your Workflow
The creation and storage of the CoD should be a standard, non-negotiable step in your IT asset disposition process.
- Initiation: The process begins when a device is slated for retirement.
- Inventory: The device's details (serial number, asset tag) are recorded in a disposition log.
- Destruction: The device is destroyed by an internal team or a third-party vendor.
- Certification: The CoD is generated, referencing the disposition log.
- Filing: The completed certificate is filed in a secure, centralized location.
Step 4: Secure Storage and Retrieval
A Certificate of Destruction is a vital legal and compliance record. It should be stored for a period defined by your industry's regulations and your company's record retention policy, which could be seven years or longer. Store digital copies in a secure, backed-up, and access-controlled repository. If you retain physical copies, they should be kept in a secure, fireproof location. The ability to retrieve a specific certificate quickly during an audit is paramount.
Common Pitfalls to Avoid with Destruction Certificates
Even with a good template, mistakes can undermine the value of a Certificate of Destruction. Being aware of common pitfalls can help you maintain the integrity of your data disposal program.
Vague or Incomplete Information
A certificate that says "destroyed one box of hard drives" is worthless. The document must be specific, with a detailed list of every serialized asset. Similarly, the method of destruction must be clearly defined (e.g., "shredded to 2mm particles in compliance with NIST 800-88"), not just "destroyed."
Accepting a Generic "Certificate of Recycling"
There is a critical difference between a Certificate of Destruction and a Certificate of Recycling. A recycling certificate only confirms that the electronic waste was processed in an environmentally responsible way. It makes no guarantee about the data on the drives. Always insist on a document that explicitly states "Destruction" and details the data sanitization method.
Not Verifying the Vendor
A certificate is only as trustworthy as the company issuing it. Before engaging an ITAD vendor, verify their credentials. Look for a NAID AAA Certification, which is the industry's leading standard for data destruction. A certified vendor is subject to rigorous, unannounced third-party audits, which ensures their processes, security, and documentation are sound. A certificate from an uncertified vendor may not hold up under legal scrutiny.
Failing to Maintain Records
Generating the certificate is only half the battle. If you cannot produce it upon request during an audit or legal proceeding, it is as if it never existed. Implement a robust record-keeping policy to ensure these vital documents are securely stored and easily retrievable for their entire retention period.
Conclusion
A Certificate of Destruction is a cornerstone of any responsible data security and IT asset management program. It is the final handshake that closes the lifecycle of a data-bearing asset, providing irrefutable proof that sensitive information has been permanently and securely eliminated. By serving as a formal audit trail, it empowers organizations to meet stringent regulatory compliance requirements, mitigate the catastrophic risks of a data breach, and transfer liability.
Using a comprehensive Hard Drive Destruction Certificate Template is the first step toward creating this vital documentation. However, the template itself is only a tool. Its ultimate value depends on the accuracy of the information it contains, the integrity of the destruction process it documents, and the reliability of the vendor who signs it. By ensuring every key component is present—from unique serial numbers to the specific method of destruction—you transform a simple document into a powerful shield for your organization. In the end, a proper CoD is not an administrative burden; it is an essential investment in security, compliance, and peace of mind.
0 Response to "Secure Hard Drive Destruction Certificate Template"
Posting Komentar